Pluck w00t!
Time to Pluck!
Though a bit late, I decided to give this machine a try!
As with all almost every machine I began with arp-scan/netdiscover:
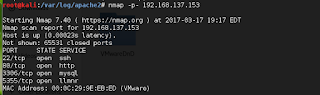
Once this is done, next I try to do a port scan on the host.
I began with the tcp scan while upd scans taking more time ran in the background.
Since port 80 was open, I ran nikto in other window.
Post this is done, I move next to check banners on each service.
SSH dint give any banner, neither mysql or llmnr protocol so I tried to enumerate the web.
Just before I went to check the web service, I looked at the nikto results and they were interesting!
Now, this was very interesting, an LFI!!
Meanwhile I had also tried fuzzing the admin page on the webservice and it revealed sql injection:
Now, I had two vectors so I thought lets begin with the LFI.
Doing a /etc/passwd dumped all the contents!!
But Trying lfi on other files like apache logs etc was not getting possible (permission issue??)
This was when something caught my eye.... There was an entry in /etc/passwd called backup-user!
Moreover, there was a script to it!
Reading the same script revealed another gateway.
Tftp was going to come in picture but is it open! Dang! Nmap for udp scan showed me port 69 for tftp was open!
Next I just get the backup file!
Now checking the backup.tar file I see /home directory. Looking further there are ssh keys in paul's directory. I make permissions changes in the keys and try one by one all 4 private keys.
key number 4 works for me and I login, but login is not a shell but a command line menu :D
Next step, I look at the various options but Edit file caught my eye! The editor was vi editor in this case. So I can do a shell escape sequence.
set shell=/bin/bash
:shell
And I get interactive session!
Next priv escalation!
I see its a very new kernel.
Searching exploits for this kernel gave me one DoS exploit but that wont work. I have to r00t!
Checking file permissions I see setuid bit on exim! That could be one vector (maybe???)
However, I thought why not try kernel exploits and dirtycow was a pure random guess!
And it worked!
w00t w00t!
And flag is captured!
Overall an awesome machine and very satisfying! Reminds me of my oscp frustration days!
Thanks vulnhub 4 hosting and @ryanoberto for making this VM!
-n!ghtcr4wl3r
Though a bit late, I decided to give this machine a try!
As with all almost every machine I began with arp-scan/netdiscover:
Once this is done, next I try to do a port scan on the host.
I began with the tcp scan while upd scans taking more time ran in the background.
Since port 80 was open, I ran nikto in other window.
Post this is done, I move next to check banners on each service.
SSH dint give any banner, neither mysql or llmnr protocol so I tried to enumerate the web.
Just before I went to check the web service, I looked at the nikto results and they were interesting!
Now, this was very interesting, an LFI!!
Meanwhile I had also tried fuzzing the admin page on the webservice and it revealed sql injection:
Now, I had two vectors so I thought lets begin with the LFI.
Doing a /etc/passwd dumped all the contents!!
But Trying lfi on other files like apache logs etc was not getting possible (permission issue??)
This was when something caught my eye.... There was an entry in /etc/passwd called backup-user!
Moreover, there was a script to it!
Reading the same script revealed another gateway.
Tftp was going to come in picture but is it open! Dang! Nmap for udp scan showed me port 69 for tftp was open!
Next I just get the backup file!
Now checking the backup.tar file I see /home directory. Looking further there are ssh keys in paul's directory. I make permissions changes in the keys and try one by one all 4 private keys.
key number 4 works for me and I login, but login is not a shell but a command line menu :D
Next step, I look at the various options but Edit file caught my eye! The editor was vi editor in this case. So I can do a shell escape sequence.
set shell=/bin/bash
:shell
And I get interactive session!
Next priv escalation!
I see its a very new kernel.
Searching exploits for this kernel gave me one DoS exploit but that wont work. I have to r00t!
Checking file permissions I see setuid bit on exim! That could be one vector (maybe???)
However, I thought why not try kernel exploits and dirtycow was a pure random guess!
And it worked!
w00t w00t!
And flag is captured!
Overall an awesome machine and very satisfying! Reminds me of my oscp frustration days!
Thanks vulnhub 4 hosting and @ryanoberto for making this VM!
-n!ghtcr4wl3r










👍
ReplyDeleteThis comment has been removed by the author.
ReplyDelete